Enhance identity proofing
Verify identity documents’ electronic signatures through the government database.
Apply anti-spoofing biometric checks to protect from presentation attacks.
CONFIDENT ACCESS MANAGEMENT
The adaptable MFA ensures access only through valid identity documents, creating a trusted digital identity. Elevate pre-verification to an even higher standard with additional watchlists (i.e., Refinitiv).

CONSISTENt ACCURACY in verification
Mob.id relies on encrypted passport chip data for accurate identity checks. It ensures trustworthy results by cross-referencing various data components such as visual information, facial photographs, and database records.
Zero knowledge architecture
Each transaction is authenticated and authorized before any action is taken. It helps to reduce the risk of unauthorized access or breaches.
Lightning-fast
On average, it takes 60 seconds to complete the identity verification. It takes seconds to authenticate using biometry.
AML Monitoring
Identity verification extended with watchlist review.
PEP, adverse media, and other sources to protect your business from fraudsters and help to avoid AML fines.
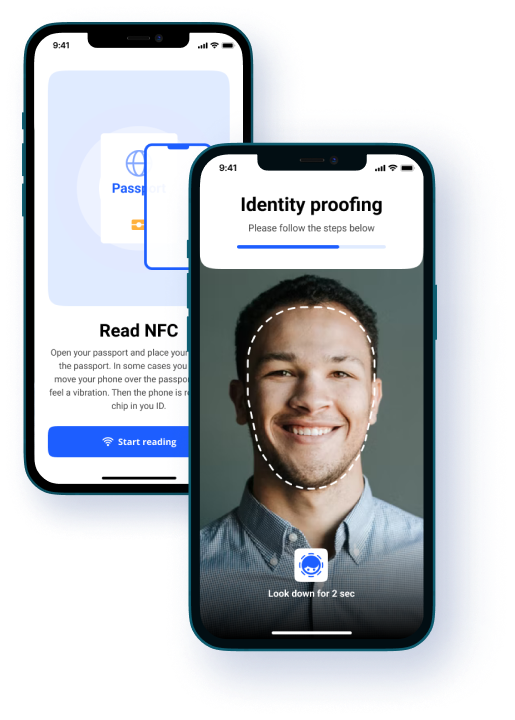
NPKD as the trust centre
National Public Key Directory (NPKD) grants the secure authentication. The authenticity and integrity of identity documents are verified against the government database.
Liveness detection with foundation
Document photographs are compared with real-time frames. AI liveness detection helps to prevent identity fraud.
Designed to scale
The microservice architecture ready to handle increased user volumes without compromising security or performance.
Decentralized and secure
Digital identity in the phone lets clients control their personal information ensuring data privacy and security.
Compliant
CCPA, GDPR, and MiCA-ready. The system adheres to the latest regulatory requirements, to comply with data protection and identity verification standards.
Seamless integration
Businesses can benefit from using API or mobile SDK in their workflow. They also can refer to the native mobile app.
Get our E-book Dedicated
EU identity walet
In this e-book, Frans Bolk, the creator of Mob.id, shares his thoughts on the European identity wallet and how it will impact European verification procedures.
Get our E-book Dedicated
EU identity walet
In this e-book, Frans Bolk, the creator of Mob.id, shares his thoughts on the European identity wallet and how it will impact European verification procedures.
Get our E-book Dedicated
EU identity walet
In this e-book, Frans Bolk, the creator of Mob.id, shares his thoughts on the European identity wallet and how it will impact European verification procedures.
Mob.id in various industries
Comprehensive AML risk management
- Global regulatory lists
- PEP
- Global sanctions list
- russians
Enhance the security of your business. Each user’s identity can be screened using the World-Check Risk Intelligence database.
- Global regulatory and law enforcement lists
- PEP
- Global sanctions list
- russians
Comprehensive AML Risk management
- Global regulatory lists
- PEP
- Global sanctions list
- russians
Enhance the security of your business. Each user’s identity can be screened using the World-Check Risk Intelligence database.
Comprehensive risk management
Enhance the security of your business. Each user’s identity can be screened using the World-Check Risk Intelligence database.
- Global regulatory lists
- PEP
- Global sanctions list
- russians
implement Mob.id in three steps
| Get a free trial license and let our back-end team set up your account. | |
| Review the documentation and implement SDK into your mobile app. Or use API for your convenience. | |
 |
Test and launch fast enhanced protection for your audience. |

Implement mob.id in three steps
| Get a free trial license and let our back-end team set up your account. | |
| Review the documentation and implement SDK into your mobile app. Or use API for your convenience. | |
 |
Test and launch fast enhanced protection for your audience. |


Implement Mob.id in three steps
 |
Get a free trial license and let our back-end team set up your account. |
 |
Review the documentation and implement SDK into your mobile app. Or use API for your convenience. |
 |
Test and launch fast enhanced protection for your audience. |
testimonials
Mob.id team helped us to identify the problems with the current authorization of my employees. In the end, we got a transparent process where the compliance officer can track each login and ensure that no one except managers has access to the admin section.
Mob.id team helped us to identify the problems with the current authorization of my employees. In the end, we got a transparent process where the compliance officer can track each login and ensure that no one except managers has access to the admin section.
Process visitors with confidence.
We thrive on challenges and are committed to providing the level of protection you desire.
Schedule a call with us to explore the full potential of Mob.id and discover how it can meet your unique security needs.
Trusted partners

Start using Mob.id now
1. Review the documentation and set up the call with our back-end team.
2. We provide the license for the organization to get ready to assist your clients.
3. Clients can start using API or mobile SDK for their businesses.
Trusted partners